Objectives:
Compute Nodes in an HPC environment are usually physically isolated from the public network and has to route through the gateway which are often found in Head Node or any delegated Node in small or small-medium size cluster to access the internet or to access company LAN to access LDAP, you can use the firewall-cmd to route the traffic through the interconnect facing the internet.
Scenario:
Traffic will be routed through the Head Node’s eno1 (internet facing) from the Head Node’s eno2 (private network). The interconnect eno1 is attached to a switch where the compute nodes are similarly attached. Some
- 192.168.1.0/24 is the private network subnet.
- 192.168.1.1 is the IP Address of the Head Node
- 155.1.1.2 is the IP Address of the external-facing ethernet ie eno1
Check the zones.
# firewall-cmd --list-all-zones
Check the Active Zones
# firewall-cmd --get-active-zones
external
interfaces: eno2
internal
interfaces: eno1
Enable masquerade at the Head Node’s External Zone
IP masquerading is a process where one computer acts as an IP gateway for a network. For masquerading, the gateway dynamically looks up the IP of the outgoing interface all the time and replaces the source address in the packets with this address.
You use masquerading if the IP of the outgoing interface can change. A typical use case for masquerading is if a router replaces the private IP addresses, which are not routed on the internet, with the public dynamic IP address of the outgoing interface on the router.
For more information. Do take a look at 5.10. Configuring IP Address Masquerading
# firewall-cmd --zone=external --query-masquerade
no
# firewall-cmd --zone=external --add-masquerade --permanent
# firewall-cmd --reload
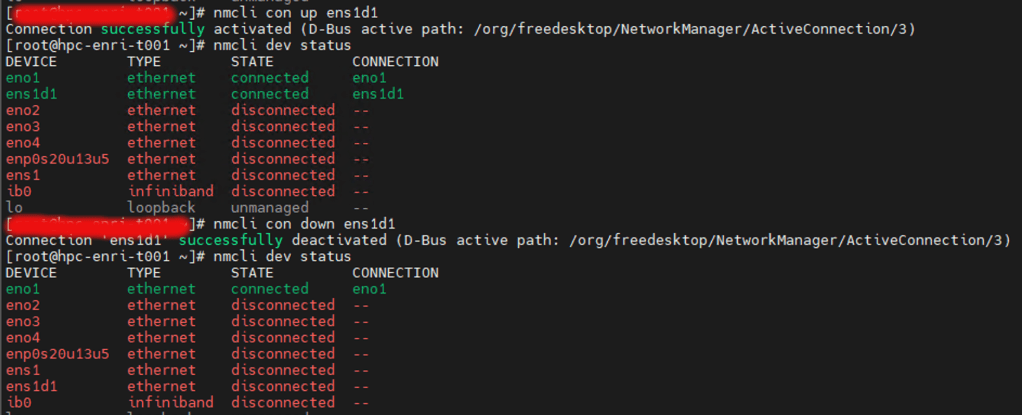
Compute Nodes at the Private Network
(Assuming that eno1 is connected to the private switch). It is very important that you input the gateway at the compute node’s /etc/sysconfig/network-scripts/ifcfg-eno1)
.....
.....
DEVICE=enp47s0f1
ONBOOT=yes
IPADDR=192.168.1.2 #Internal IP Address of the Compute Node
NETMASK=255.255.255.0
GATEWAY=192.168.1.1 #Internal IP Address of the Head Node
Next, you have to put the Network Interface of the Client in the Internal Zone of the firewall-cmd. Assuming that eno1 is also used by the Client Network
# firewall-cmd --zone=internal --change-interface=eno1 --permanent
You may want to set the selinux to disabled
# setenforce 0
Configure the Head Node’s External Zone.
For Zoning, do take a look at 5.7.8. Using Zone Targets to Set Default Behavior for Incoming Traffic
For this setting, we have chosen target “default”
# firewall-cmd --zone=external --set-target=default
You can configure other settings. For the External Zone. For example, add SSH Service, mDNS
# firewall-cmd --permanent --zone=external --add-service=ssh
# firewall-cmd --permanent --zone=external --add-service=mdns
# firewall-cmd --runtime-to-permanent
# firewall-cmd --reload
Make sure the right Ethernet is placed in the right Zone. For External-Facing Ethernet Card, (eno2), you may want to place it
# firewall-cmd --zone=external --change-interface=eno2 --permanent
For Internal Facing Ethernet Card, (eno1), you want want to place it
# firewall-cmd --zone=internal --change-interface=eno1 --permanent
Configure the firewall-Source of Internal Network (eno1)
# firewall-cmd --zone=internal --add-source=192.168.1.0/24
Checking the Settings in the “firewall-cmd –get-active-zones”
# firewall-cmd --get-active-zones
internal (active)
target: default
icmp-block-inversion: no
interfaces: eno1
sources: 192.168.1.0/32
services: dhcpv6-client mdns ssh
ports:
protocols:
forward: no
masquerade: no
forward-ports:
source-ports:
icmp-blocks:
rich rules:
public (active)
target: default
icmp-block-inversion: no
interfaces: eno2
sources:
services: dhcpv6-client ssh
ports:
protocols:
forward: no
masquerade: yes
forward-ports:
source-ports:
icmp-blocks:
rich rules:
Check the Firewall Status
systemctl status firewalld.service